Abstract
Counterfeiting affects diverse industries, including pharmaceuticals, electronics, and food, posing serious health and economic risks. Printable unclonable codes, such as Copy Detection Patterns (CDPs), are widely used as an anti-counterfeiting measure and are applied to products and packaging. However, the increasing availability of high-resolution printing and scanning devices, along with advances in generative deep learning, undermines traditional authentication systems, which often fail to distinguish high-quality counterfeits from genuine prints.
In this work, we propose a diffusion-based authentication framework that jointly leverages the original binary template, the printed CDP, and a representation of printer identity that captures relevant semantic information. Formulating authentication as multi-class printer classification over printer signatures lets our model capture fine-grained, device-specific features via spatial and textual conditioning. We extend ControlNet by repurposing the denoising process for class-conditioned noise prediction, enabling effective printer classification.
On the Indigo Base dataset, our method outperforms traditional similarity metrics and prior deep learning approaches, while generalizing to counterfeit types unseen during training.
Problem Setting
Authentication is formulated as printer-class prediction under multimodal conditioning.
- Binary template supplies structural reference.
- Printed CDP supplies spatial printer-specific degradation.
- Printer identity text supplies class-level semantic conditioning.
A candidate is accepted as authentic only if predicted printer identity matches the known source printer.
Visual Overview: Problem To Solution
Figure 1: Failure Case For Similarity-Based Authentication
The left side starts from the binary template and authentic print. The right side shows counterfeit prints obtained after estimation attacks. Even when counterfeit quality is high, score-based checks such as NCC can remain deceptively high, which motivates moving from direct similarity scoring to printer-aware classification.
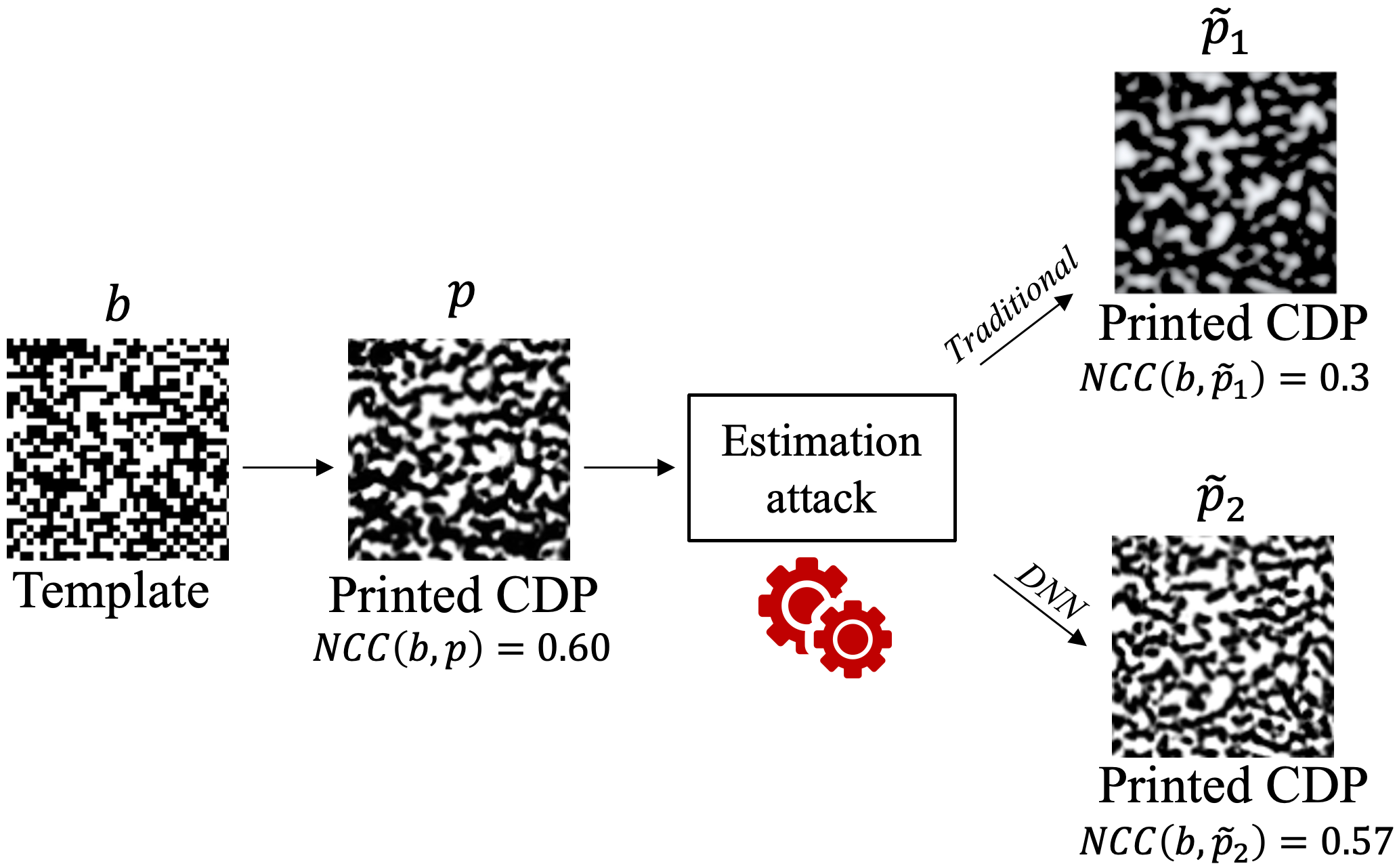
Threat model and failure mode: deep-learning-based counterfeits can preserve high structural similarity, making thresholded metrics less reliable.
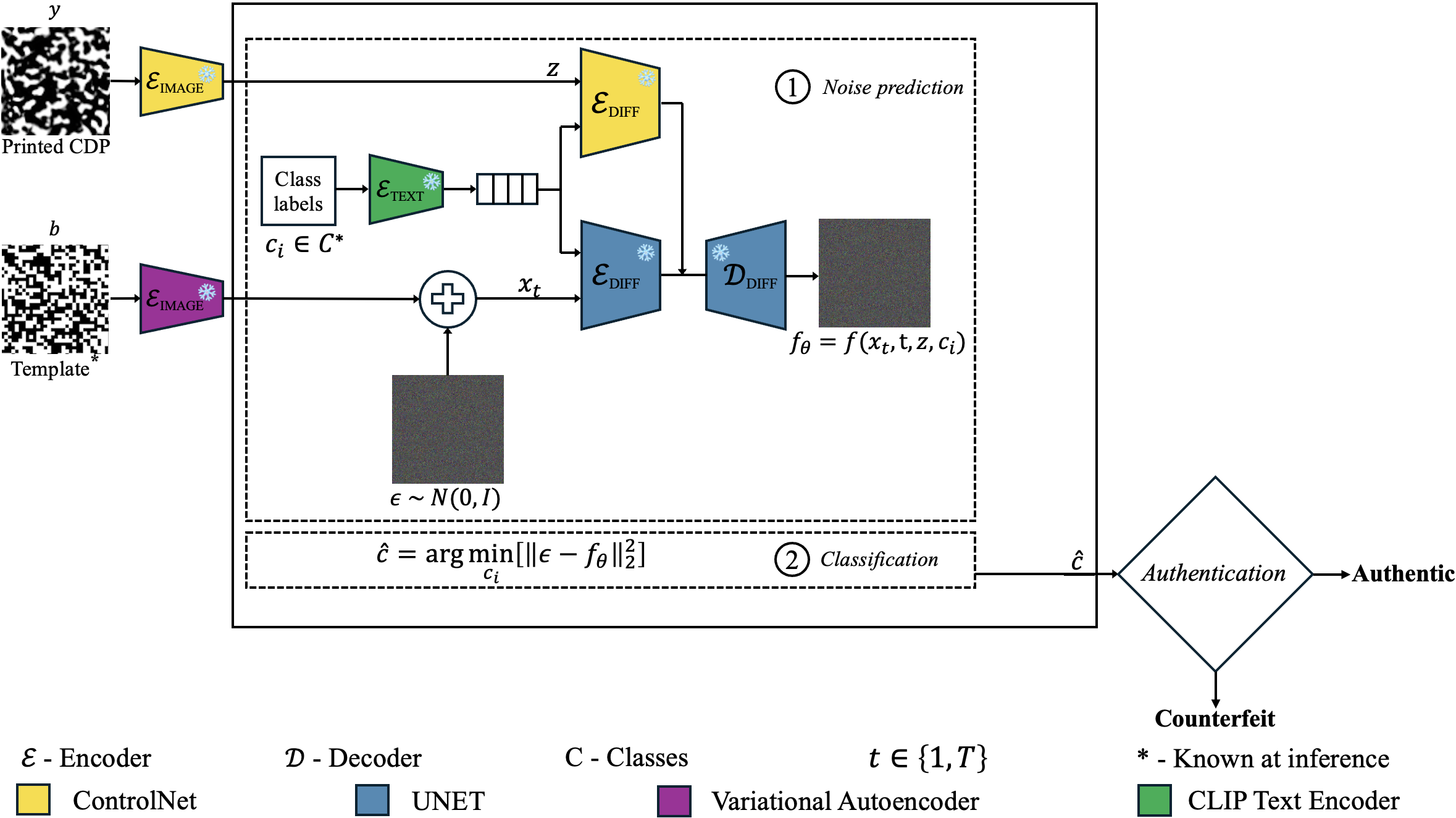
Figure 2: Printer-Conditioned Diffusion Authentication Pipeline
This pipeline takes the noised template latent and conditions denoising on both the printed CDP (spatial signal) and printer identity (class signal). The model predicts noise for each candidate class and selects the class with minimum reconstruction error, then authenticates only if the predicted class matches the expected source printer.
Interactive Figure 2 Walkthrough
Click through the pipeline stages to highlight where each operation happens in the architecture.
Highlight box follows the selected step.
Step 1
Step 1: Build Joint Conditioning
The noised latent is conditioned with printed-CDP spatial features and printer-identity text features to expose both local texture and class semantics.
Authentication Strategy Simulator
Simulates the final policy: authenticate only when predicted class equals expected authentic printer.
Rule Logic
- Select expected authentic printer label.
- Use model output as predicted class label.
- Accept only if labels match exactly.
HP55 == HP55
Match -> Authentic
Decision
Counterfeit
Predicted class: HP55
Expected class: HP55
Predicted class does not match expected printer.
Key Insight
A printer’s physical signature is embedded in how the binary template is degraded through printing and scanning. A diffusion model that can reverse this degradation for each class reconstructs accurately only when conditioned on the correct class, turning denoising quality into an authentication signal.
Results At A Glance
Lower is better for all three metrics. The chart summarizes the overall error profile used in the detailed tables below.
Method Comparison (Authentication Error)
| Method | P_err | P_miss (HP55) | P_miss (HP76) | P_miss mean | P_fa (HP55_55) | P_fa (HP55_76) | P_fa (HP76_76) | P_fa (HP76_55) | P_fa mean |
|---|---|---|---|---|---|---|---|---|---|
| NCC | 0.286 | 0.292 | 0.310 | 0.301 | 0.300 | 0.361 | 0.264 | 0.201 | 0.273 |
| SSIM | 0.275 | 0.264 | 0.300 | 0.281 | 0.292 | 0.285 | 0.292 | 0.210 | 0.269 |
| Chaban et al. (retrained) | 0.091 | 0.125 | 0.111 | 0.118 | 0.097 | 0.160 | 0.000 | 0.000 | 0.064 |
| Ours | 0.023 | 0.049 | 0.035 | 0.005 | 0.000 | 0.014 | 0.007 | 0.000 | 0.042 |
Classification Analysis
| Actual \\ Pred | HP55 | HP76 | HP55_55 | HP55_76 | HP76_76 | HP76_55 |
|---|---|---|---|---|---|---|
| HP55 | 95 | 5 | 0 | 0 | 0 | 0 |
| HP76 | 3 | 97 | 0 | 0 | 0 | 0 |
| HP55_55 | 0 | 0 | 83 | 15 | 1 | 1 |
| HP55_76 | 1 | 0 | 14 | 83 | 1 | 1 |
| HP76_76 | 0 | 1 | 1 | 1 | 89 | 8 |
| HP76_55 | 0 | 0 | 2 | 2 | 19 | 77 |
The confusion matrix shows very strong separation for authentic classes (95-97%). Most confusion occurs among counterfeit subclasses, which has limited impact on final authentication because acceptance requires matching the expected authentic printer class.
Generalization to Unseen Counterfeits
| Counterfeit type group | P_err | P_miss | P_fa |
|---|---|---|---|
| Known counterfeit | 0.012 | 0.024 | 0.000 |
| Unknown counterfeit | 0.012 | 0.024 | 0.000 |
Ablations And Reconstruction
Binary Template Reconstruction (VAE)
| Configuration | Avg. MSE |
|---|---|
| Pretrained VAE | 0.581 |
| Fine-tuned VAE | 0.075 |
Ablation: Template Input
| Input configuration | P_err | P_miss | P_fa |
|---|---|---|---|
| No template input | 0.660 | 0.430 | 0.200 |
| With template input | 0.023 | 0.042 | 0.005 |
Ablation: Printer Identity Representation
| Representation | P_err | P_miss | P_fa |
|---|---|---|---|
| Printer index-based | 0.521 | 0.962 | 0.082 |
| Appearance-based text | 0.035 | 0.063 | 0.001 |
| Printer information text | 0.023 | 0.042 | 0.005 |
Contributions
- First unified CDP authentication framework combining binary template, printed CDP, and printer identity conditioning.
- ControlNet extension from generation to class-conditioned classification by per-class noise prediction.
- Multi-printer authentication setting that captures printer-specific signatures in one model.
Future Work
- Authentic-only training without requiring counterfeit samples.
- Scaling evaluation to larger printer sets and broader hardware diversity.
- Robustness validation across varied acquisition pipelines, scanners, and capture resolutions.
BibTeX
@inproceedings{atoki2026diffusioncdp, title={Diffusion-Based Authentication of Copy Detection Patterns: A Multimodal Framework with Printer Signature Conditioning}, author={Atoki, Bolutife and Tkachenko, Iuliia and Kerautret, Bertrand and Crispim-Junior, Carlos}, booktitle={Proceedings of the IEEE/CVF Winter Conference on Applications of Computer Vision (WACV)}, year={2026}}